Ransomware: lessons all companies can learn from the British Library attack
In October 2023, the British Library suffered "one of the worst cyber incidents in British history," as described by Ciaran Martin, ex-CEO of the National Cyber Security Centre (NCSC).
The notorious Rhysida ransomware gang broke into one of the world's greatest research libraries, encrypting or destroying much of its data, and exfiltrating 600 GB of files, including personal information of British Library staff and users.
This wasn't the type of cyber attack that can be easily glossed over. The British Library's enormous trove of data - with over 170 million items, including 13 million printed and electronic books, plus hundreds of thousands of periodicals, microfilms, and rare manuscripts - is used by researchers around the world.
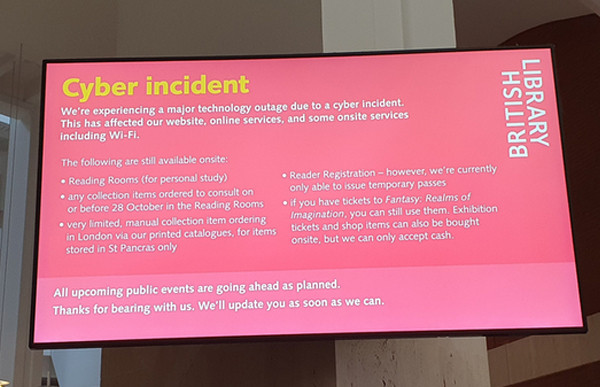
Visitors to the library - online or in-person - were left in no doubt of the scale of the problem.
Meanwhile, the Rhysida hacking group demanded a ransom of 20 Bitcoin (approximately £600,000 at the time) for decryption keys and the return of the stolen data.
The British Library, however, announced that it had chosen not to have any contact with the Rhysida gang, let alone pay the ransom:
The library has not made any payment to the criminal actors responsible for the attack, nor engaged with them in any way. Ransomware gangs contemplating future attacks such as this on publicly-funded institutions should be aware that the UK's national policy, articulated by NCSC, is unambiguously clear that no such payments should be made.
British Library
- Enhance network monitoring capabilities: Legacy network technology may need to be upgraded to ensure that advanced security tools can benefit from full visibility of the network.
- Retain on-call external security specialists: Having expert external security advice on retainer allows for additional resilience, improved speed of response, and depth of analysis in the earliest stages of an incident.
- Fully implement multi-factor authentication: Mandate MFA across all internet-facing systems, including supplier endpoints.
- Enhance intrusion response processes: Conduct thorough security reviews after even the slightest sign of network intrusion in order to prevent attackers from regaining a foothold.
- Implement network segmentation: Compartmentalise networks to minimise the potential impact of breaches.
- Practice comprehensive business continuity plans: Regularly practice attack scenarios for maximum preparedness.
- Maintain a holistic overview of cyber-risk: Routinely escalate all IT risks to senior management, ensuring their understanding for informed decision-making.
- Modernize systems, eliminate legacy technology: 'Legacy' systems are not just hard to maintain and secure, they are extremely hard to restore. Prioritise continuous investment in modern systems for security and recoverability.
- Prioritise remediation of issues arising from legacy technology: Address issues stemming from outdated technology as a matter of urgency throughout the organisation.
- Prioritise recovery alongside security: Yes, you should invest in preventative measures, but you also need to ensure that you have the capability to rapidly restore systems if an attack should happen.
- Cyber-risk awareness and expertise at senior level: Improve cyber-risk understanding among senior leadership for strategic investment; consider putting in place a dedicated expert to sit on the board or advise it.
- Regularly train all staff in evolving risks: Provide role-specific, up-to-date cybersecurity training for all employees.
- Proactively manage staff and user wellbeing: Include provisions for managing staff and user wellbeing in the aftermath of an attack, some of whom may have had their data compromised or their work disrupted.
- Review acceptable personal use of IT: Update acceptable use policies to enforce personal data security best practices. The level of intrusion into the lives of individual staff members can be exacerbated where the use of network storage is allowed for personal use.
- Collaborate with sector peers: Share insights and threat intelligence within your sector to stay informed about common threats and best cybersecurity practices.
- Implement Government standards, review and audit policies and processes regularly: Meet minimum cybersecurity standards and conduct frequent policy and process reviews. The British Library says it was accredited Cyber Essentials Plus from 2019 until 2022, when changes to the standard meant that it ceased to be compliant pending replacement of some of its legacy core systems. It says its new infrastructure will be built to Cyber Essentials Plus standard in recovery.
The Rhysida hacking group published the stolen data on the dark web after failing to secure the ransom of 20 bitcoin that it had demanded.
The decision as to whether ransomware-hit organisations should pay a ransom or not is a complex one.
In a perfect world, if no-one ever paid the ransom, there wouldn't be an incentive for ransomware gangs to attack companies. Criminals would look for other ways to make their fortunes, and hacking gangs would simply determine it wasn't worth launching ransomware attacks.
Unfortunately, the world isn't perfect. Some organisations will feel that they have no choice but to make the painful difficult decision to pay their attackers. It's not that paying your extortionists is a good thing to do, but it might well be the pragmatic less worse thing for a business to do if it can see no other way to continue operating.
Five months later, while its buildings have remained open, the British Library's online systems and services remain profoundly affected. Users cannot even change the passwords they have previously used to access British Library services.
The rebuild of the British Library's infrastructure is expected to be completed by mid-April. After that, it will begin to restore systems in a phased roll-out.
Now, in an admirable display of transparency, the British Library has published a detailed report into the cyber attack, the lessons it has learnt, and detailed the struggles it has faced renewing its complex legacy infrastructure to better secure itself into the future.
Is your company ready for a ransomware attack?
Many organisations underestimate the importance of having a robust incident response plan. But knowing how to respond, especially in those critical first 48 hours after a cyber attack, can be critical.
Do you worry your company won't know how to recover after a cyber attack? Has your business just been hit by ransomware and you're wondering what to do?
There's still hope.
Don't make the mistake of believing that your organisation will never be targeted. The right approach is to take proactive measures in advance - as it's not a case of whether your business will suffer the likes of a ransomware attack but when.
Make sure to read Exponential-e's step-by-step guide on ransomware remediation.
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.